Writing · 14 posts
Blog
Lab writeups and technical deep dives.What I learned, written down so I'll remember it.
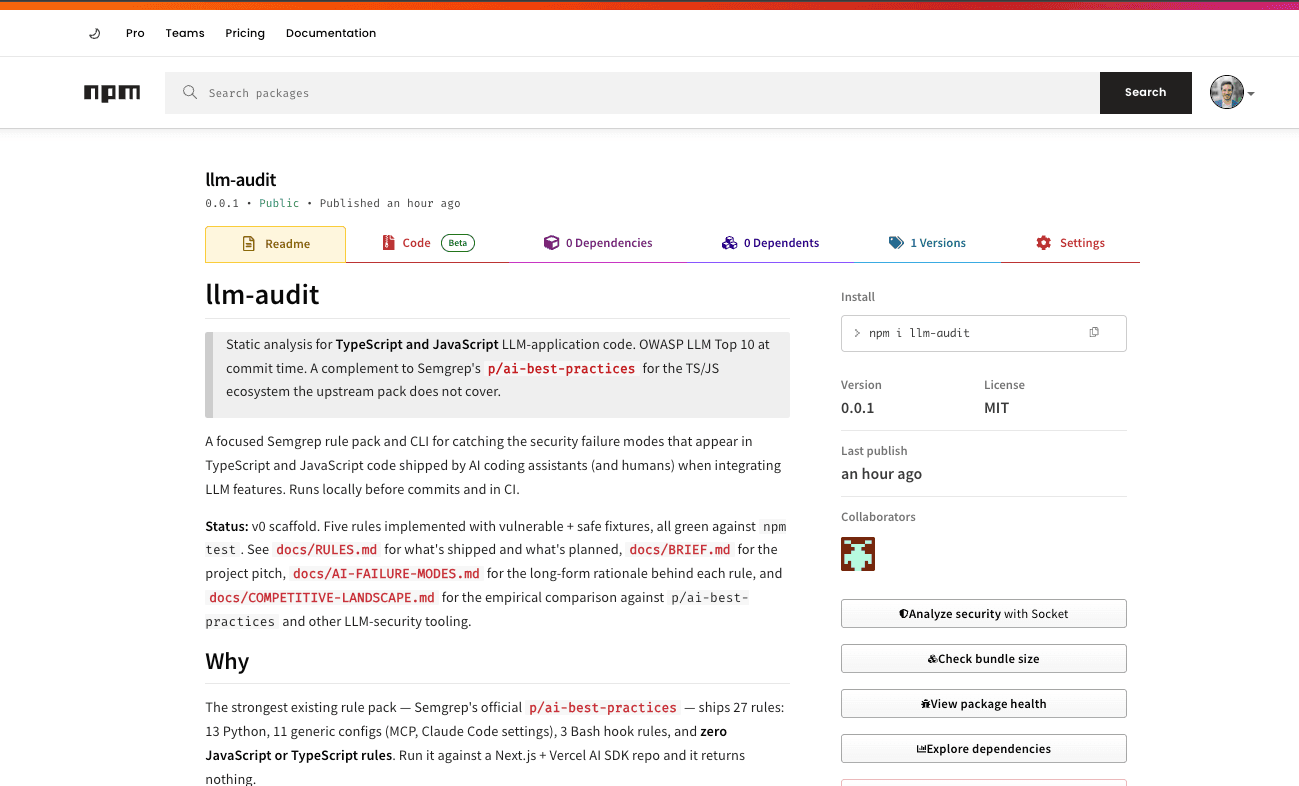
Building llm-audit: TypeScript Static Analysis for LLM Applications
Why I built a Semgrep rule pack for OWASP LLM Top 10 in TypeScript and JavaScript, and how it found a real LLM02 Insecure Output Handling bug in my own portfolio.

PowerShell for Speed and Scale: Fleet-Wide Hunting with Invoke-Command, Event ID 7045, and Get-FileHash
A hands-on PowerShell workflow spanning local process/service enumeration through the object pipeline (Get-Process, Get-Service, Where-Object, Measure-Object, Out-GridView, Export-Csv), remote execution across three alpha-svr hosts with Invoke-Command, and a concrete hunt that surfaces a rogue BrokerSvc running broker.exe as LocalSystem — complete with Event ID 7045 correlation and a SHA-256 suitable for IOC distribution.

Applying Windows Security Policies with secedit.exe: Analyze, Configure, and Verify Baseline Compliance
A hands-on walkthrough of Windows baseline compliance using secedit.exe /analyze and /configure: comparing a VM to the Alpha basic security template, surfacing MinimumPasswordLength, LockoutBadCount, and MaximumLogSize drift via PowerShell Select-String, applying the template, and re-analyzing to produce before/after audit evidence.